Every character we type on the terminal is sent in a single IP Packet, right, a single packet is used for every character.
A quick look at Wireshark capture shows the below.
Above 3 rows shows the initial 3-way handshake for TCP. It is followed by several Telnet own internal commands.
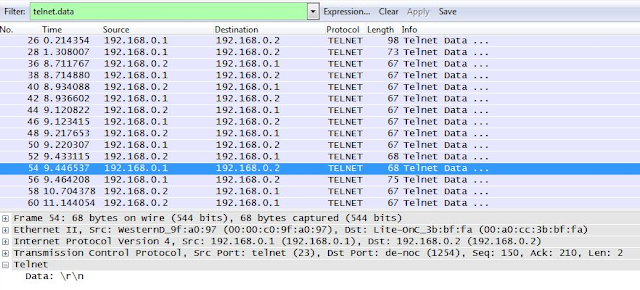
To look at the actual user data, we need to add a wireshark filter "telnet.data", this filters all lines for the ones with the user data.
Here we can see the filter applied and all the lines that has user data. The first selected row shows the Telnet server's OS details and the pseudoterminal interface ttyp1.
After presenting that, 192.168.0.1 asks for login id.
We type the login id "fake" and press enter.
As we can see, even though we typed the complete user id "fake", it won't be transmitted as-a-whole in the actual communication, rather, each character is transmitted, in the above, it is "f", followed by "a" in the below.
Even the Carriage Return (Enter) is transmitted in a single packet from the source to the destination (below)
Destination replies back with a Carriage Return + New Line, and later, with the Password prompt.
Headers/banners from the Telnet server is communicated in single packets, however, user input and telnet server's output is communicated as one character per-packet.
I believe this was designed like this to address the problem with low bandwidth networks of old days, irrespective of the overhead (66 Bytes) it carries for a single character payload (1 Byte).
Considering modern networks where bandwidth is not a concern any more from the perspective of Telnet communications, I think the protocol needs to be redesigned.
But the question should be asked, which sane person uses a clear text protocol for authentication?






Play Emperor Casino Online for real money now!
ReplyDeleteGet a chance to play 샌즈카지노 some amazing games like Emperor Casino. Try a free version for 제왕 카지노 real money at ShootEmCasino, where you can play against 메리트 카지노 주소 other players,